Microsoft’s business social network, LinkedIn, is the target of a fake job offer campaign being used to spam users’ inboxes and drop malware on their devices.
Security company, Proofpoint, explains that the purpose of this attempt by cybercriminals is to deliver the More_eggs backdoor, which acts as a downloader, allowing attackers to deploy malware on the compromised host.
The firm says the malicious actors use ordinary looking LinkedIn profiles they create to reach out to their potential targets through short messages that highlight job opportunities.
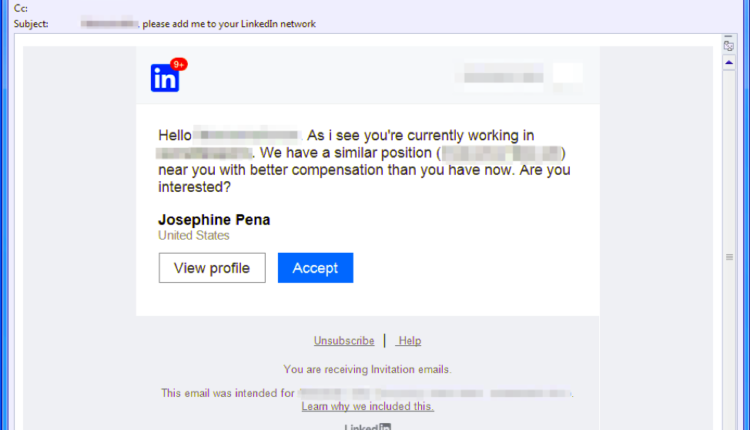
These hackers return a few days later with direct emails to the work address given on LinkedIn to direct their targets to websites they claim host detailed information on the purported job ad.
Proofpoint researchers noted that the URLs given link to a landing page akin to that of a legit talent and staffing management company, even using stolen branding to enhance the campaign’s legitimacy.
These URLs may include PDF documents with fake details of the job, and point to malicious URLs.
Once the malware is downloaded, the website downloads a malicious Microsoft Word document laden with macros that are crafted specifically to download the More_eggs backdoor.
The fake campaign can get more complex, even using URL shorteners, password-protected Microsoft Word documents, or other attachments, depending on the attack.
Proofpoint explains that even “completely benign emails without malicious attachments or URLs” in an attempt to establish rapport further.
“This actor provides compelling examples of these new approaches, using LinkedIn scraping, multi-vector and multi-step contacts with recipients, personalized lures, and varied attack techniques to distribute the More_eggs downloader, which in turn can distribute the malware of their choice based on system profiles transmitted to the threat actor,” they added.
How to stay protected
The trick is to ignore such messages that point you to suspicious-looking websites, or that include attachments that pose risks of infection.
Additionally, make sure your security tools are always up-to-date.
